
According to the police, "fraudsters are posing as government officials in order to trick people into installing ransomware which encrypts files on victims’ computers."
Further to our previous advice on ransomware, please be aware that schools are receiving phone calls from fraudsters posing as 'Department of Education' officials who do the following:- Request an email address for a key member of staff in order to forward 'guidance forms'
- After obtaining the email address they send an email with a zip file attachment infected with ransomware
- Once the attachment has been downloaded the ransomware locks and encrypts computer files and asked for a ransom of up to £8,000 to regain access.
What should schools do?
- Be vigilant about Vishing ('Voice phishing') phone calls
- Only share email addresses with trusted sources
- Do not open any files attached to an email unless you know what it is
- Update your anti-virus software regularly
- Be prepared. Backup school files offsite on a regular basis
How can SBS help?
Service Desk support
If you are concerned that you have been targeted by ransomware, please call us on 0345 222 1551 • Option 1 (existing ICT customers) or 0345 222 1551 • Option 5 (non-ICT customers).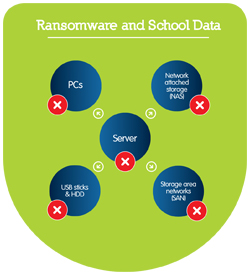
Once it has targeted your server, the ransomware will seek and infect all onsite data storage, as depicted above.
Disaster Recovery Solution - Be proactive and backup your data offsite
The safeguarding of critical data is our primary concern and we don't want schools paying to get their files back. With this in mind we have developed a Disaster Recovery Solution to backup, secure and restore data in the event of an attack from ransomware. For more information, call 0345 222 1551 • Option 5 or email us, and we can recommend the amount of storage you need to backup your files offsite and out of reach of virtual threats.Get sector Insights delivered straight to your inbox.
Subscribe to to the SBS Blog and never miss an update.

